Cybersecurity is not simply the area of the IT employees placing in firewalls and backing up servers. It takes a dedication from the highest and a finances to match. The stakes are excessive with regards to retaining your prospects’ info protected.
The common value of an information breach in 2018 was $148 for every compromised document. That equals a median value of $3.86 million per breach. Because it takes organizations greater than six months—196 days on common—to detect breaches, numerous remediation should occur after discovery.
With compliance laws in most industries tightening and stricter safety guidelines, such because the General Data Protection Regulation (GDPR) turning into regulation, breaches can result in massive fines in addition to lack of repute.
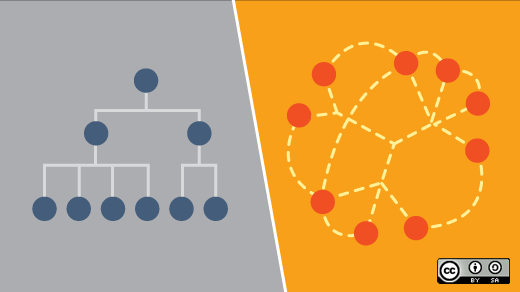
To construct a cybersecurity answer from the highest down, you could construct a strong basis. This basis must be considered not as a expertise downside however as a governance concern. Tech options will play a task, nevertheless it takes greater than that—it begins with constructing a tradition of security.
Build a cybersecurity tradition
“A chain is no stronger than its weakest link,” Thomas Reid wrote again in 1786. The message nonetheless applies with regards to cybersecurity as we speak. Your techniques are solely as safe as your least safety-conscious workforce member. One lapse, by one particular person, can compromise your information.
It’s essential to construct a tradition the place all workforce members perceive the significance of cybersecurity. Security isn’t just the IT division’s job. It is everybody’s duty.
Training is a steady duty. When new workforce members are on-boarded, they must be educated in safety finest practices. When workforce members depart, their entry should be restricted instantly. As workforce members get snug of their positions, there must be strong policies, procedures, and training to maintain them security acutely aware.
Maintain safe techniques
Corporate insurance policies and procedures will set up a safe baseline to your techniques. It’s essential to take care of strict adherence as techniques broaden or evolve. Secure community design should match these insurance policies.
A safe system will be capable of filter all incoming visitors on the community perimeter. Only visitors required to help your group must be allowed to get via this perimeter. Unfortunately, threats typically nonetheless get in.
Zero-day assaults are growing in quantity, and extra risk actors are exploiting recognized defects in software program. In 2018, greater than three-quarters of successful endpoint attacks exploited zero-day flaws. While it is tough to protect towards unknown threats, you may decrease your publicity by strictly making use of updates and patches instantly after they’re launched.
Manage person privileges
By limiting every particular person person’s entry and privileges, corporations can make the most of micro-segmenting to reduce potential harm performed by a potential assault. If an assault does get via your safe perimeter, this may restrict the variety of areas the attacker has entry to.
User entry must be restricted to solely the privileges they should do their jobs, particularly with regards to delicate information. Most breaches begin with electronic mail phishing. Unsuspecting workers click on on a malicious hyperlink or are tricked into giving up their login credentials. The much less entry workers have, the much less harm a hacker can do.
Identity and entry administration (IAM) techniques can deploy single sign-on (SSO) to scale back the variety of passwords customers have to entry techniques by utilizing an authentication token accepted by completely different apps. Multi-factor authentication practices mixed with decreasing privileges can decrease threat to your entire system.
Implement steady monitoring
Your safety wants continuous monitoring across your enterprise to detect and stop intrusion. This consists of servers, networks, Software-as-a-Service (SaaS), cloud companies, cell customers, third-party purposes, and rather more. In actuality, it’s crucial that each entry level and connection are repeatedly monitored.
Your workers are working across the clock, particularly if you’re a world enterprise. They are working from house and dealing on the highway. This means a number of gadgets, web accesses, and servers, all of which must be monitored.
Likewise, hackers are working repeatedly to seek out any flaw in your system that might result in a potential cyberattack. Don’t wait to your subsequent IT audit to fret about discovering the failings; this must be a continuing course of and excessive precedence.
Conduct common threat assessments
Even with steady monitoring, chief info safety officers (CISOs) and IT managers ought to commonly conduct threat assessments. New gadgets, hardware, third-party apps, and cloud companies are being added on a regular basis. It’s simple to neglect how all these particular person items, added one after the other, all match into the massive image.
The commonly scheduled, formal threat evaluation ought to take an exhaustive take a look at infrastructure and entry factors. It ought to embrace penetration testing to establish potential threats.
Your threat evaluation also needs to analyze backups and data-recovery planning in case a breach happens. Don’t simply arrange your safety and hope it really works. Have a plan for what you’ll do if entry is breached, know who can be liable for what, and set up an anticipated timeline to implement your plan.
Pay consideration to distant groups and BYOD customers
More workforce members than ever work remotely. Whether they’re engaged on the highway, at a distant location, or from house, they pose a cybersecurity threat. They are connecting remotely, which might leave channels open for intrusion or data interception.
Team members typically combine firm gadgets and private gadgets virtually seamlessly. The introduction of BYOD (convey your individual gadget) means firm belongings might also be weak to apps and software program put in on private gadgets. While you may handle what’s on firm gadgets, when workers verify their firm electronic mail from their private cellphone or join to an organization server from their private laptop computer, you have elevated your general threat.
Personal gadgets and distant connections ought to at all times make the most of a digital non-public community (VPN). A VPN makes use of encrypted connections to the web that create a personal tunnel that masks the person’s IP tackle. As Douglas Crawford, resident safety skilled at ProPrivacy.com, explains, “Until the Edward Snowden revelations, people assumed that 128-bit encryption was in practice uncrackable through brute force. They believed it would be so for around another 100 years (taking Moore’s Law into account). In theory, this still holds true. However, the scale of resources that the NSA seems willing to throw at cracking encryption has shaken many experts’ faith in these predictions. Consequently, system administrators the world over are scrambling to upgrade cipher key lengths.”
A top-down cybersecurity technique is crucial
When it involves cybersecurity, a top-down technique is crucial to offering satisfactory safety. Building a tradition of cybersecurity all through the group, sustaining safe techniques, and steady monitoring are important to safeguarding your techniques and your information.
A top-down strategy means your IT division just isn’t solely centered in your firm’s tech stack whereas administration is solely centered on the corporate mission and goals. These are not siloed departments; they’re interwoven and depending on one another to make sure success.
Ultimately, success is outlined as retaining your buyer info protected and safe. Continuous monitoring and safety of delicate info are vital to the success of your entire firm. With high administration on board with funding cybersecurity adequately, IT can guarantee optimum safety practices.